Chinese APT41 Upgrades Malware Arsenal with DodgeBox and MoonWalk – OfficialSarkar
The China-linked advanced persistent threat (APT) group codenamed APT41 is suspected to be using an “advanced and upgraded version” of a known malware called StealthVector to deliver a previously undocumented backdoor dubbed MoonWalk.
The new variant of StealthVector – which is also referred to as DUSTPAN – has been codenamed DodgeBox by Zscaler ThreatLabz, which discovered the loader strain in April 2024.
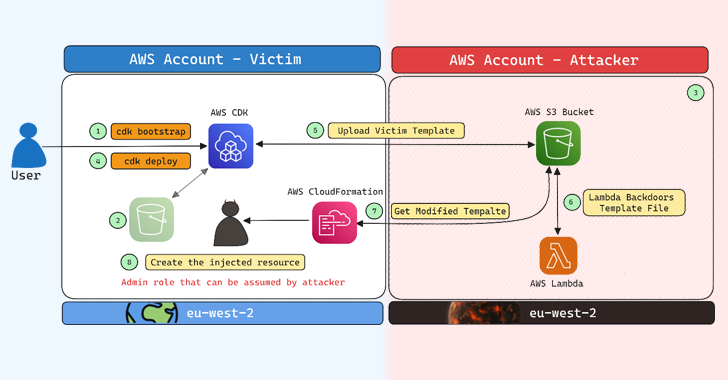
“DodgeBox is a loader that proceeds to load a new backdoor named MoonWalk,” security researchers Yin Hong Chang and Sudeep Singh said. “MoonWalk shares many evasion techniques implemented in DodgeBox and utilizes Google Drive for command-and-control (C2) communication.”
APT41 is the moniker assigned to a prolific state-sponsored threat actor affiliated with China that’s known to be active since at least 2007. It’s also tracked by the broader cybersecurity community under the names Axiom, Blackfly, Brass Typhoon (formerly Barium), Bronze Atlas, Earth Baku, HOODOO, Red Kelpie, TA415, Wicked Panda, and Winnti.
In September 2020, the U.S. Department of Justice (DoJ) announced the indictment of several threat actors associated with the hacking crew for orchestrating intrusion campaigns targeting more than 100 companies across the world.
“The intrusions […] facilitated the theft of source code, software code signing certificates, customer account data, and valuable business information,” the DoJ said at the time, adding they also enabled “other criminal schemes, including ransomware and ‘crypto-jacking’ schemes.”
Over the past few years, the threat group has been linked to breaches of U.S. state government networks between May 2021 and February 2022, in addition to attacks targeting Taiwanese media organizations using an open-source red teaming tool known as Google Command and Control (GC2).
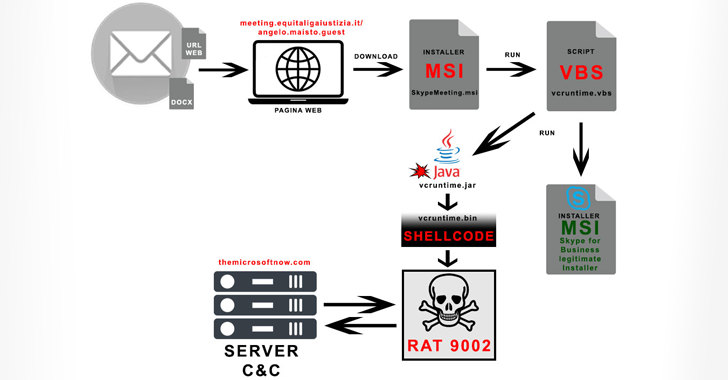
The use of StealthVector by APT41 was first documented by Trend Micro in August 2021, describing it as a shellcode loader written in C/C++ that’s used to deliver Cobalt Strike Beacon and a shellcode implant named ScrambleCross (aka SideWalk).
DodgeBox is assessed to be an improved version of StealthVector, while also incorporating various techniques like call stack spoofing, DLL side-loading, and DLL hollowing to evade detection. The exact method by which the malware is distributed is presently unknown.
“APT41 employs DLL side-loading as a means of executing DodgeBox,” the researchers said. “They utilize a legitimate executable (taskhost.exe), signed by Sandboxie, to sideload a malicious DLL (sbiedll.dll).”

The rogue DLL (i.e., DodgeBox) is a DLL loader written in C that acts as a conduit to decrypt and launch a second-stage payload, the MoonWalk backdoor.
The attribution of DodgeBox to APT41 stems from the similarities between DodgeBox and StealthVector; the use of DLL side-loading, a technique widely used by China-nexus groups to deliver malware such as PlugX; and the fact that DodgeBox samples have been submitted to VirusTotal from Thailand and Taiwan.
“DodgeBox is a newly identified malware loader that employs multiple techniques to evade both static and behavioral detection,” the researchers said.
“It offers various capabilities, including decrypting and loading embedded DLLs, conducting environment checks and bindings, and executing cleanup procedures.”
Source: TheHackerNews