Critical Flaw in Microchip ASF Exposes IoT Devices to Remote Code Execution Risk – OfficialSarkar
A critical security flaw has been disclosed in the Microchip Advanced Software Framework (ASF) that, if successfully exploited, could lead to remote code execution.
The vulnerability, tracked as CVE-2024-7490, carries a CVSS score of 9.5 out of a maximum of 10.0. It has been described as a stack-based overflow vulnerability in ASF’s implementation of the tinydhcp server stemming from a lack of adequate input validation.
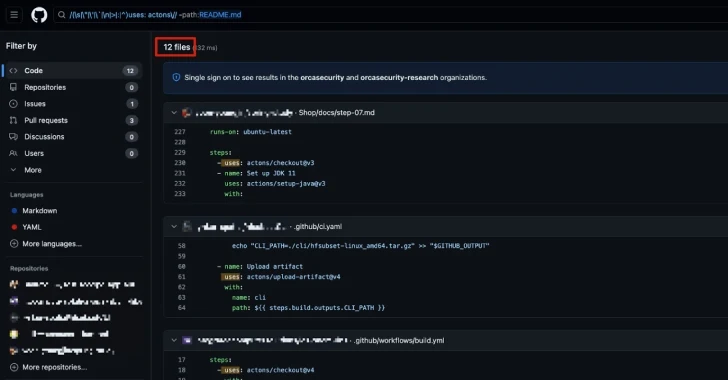
“There exists a vulnerability in all publicly available examples of the ASF codebase that allows for a specially crafted DHCP request to cause a stack-based overflow that could lead to remote code execution,” CERT Coordination Center (CERT/CC) said in an advisory.
Given that the software is no longer supported and is rooted in IoT-centric code, CERT/CC has warned that the vulnerability is “likely to surface in many places in the wild.”
The issue impacts ASF 3.52.0.2574 and all prior versions of the software, with the agency also noting that multiple forks of the tinydhcp software are likely susceptible to the flaw as well.
There are currently no fixes or mitigations to address CVE-2024-7490, barring replacing the tinydhcp service with another one that does not have the same issue.
The development comes as SonicWall Capture Labs detailed a severe zero-click vulnerability affecting MediaTek Wi-Fi chipsets (CVE-2024-20017, CVSS 9.8) that could open the door to remote code execution without requiring any user interaction due to an out-of-bounds write issue.
“The affected versions include MediaTek SDK versions 7.4.0.1 and earlier, as well as OpenWrt 19.07 and 21.02,” the company said. “This translates to a large variety of vulnerable devices, including routers and smartphones.”

“The vulnerability is a buffer overflow as a result of a length value taken directly from attacker-controlled packet data without bounds checking and placed into a memory copy. This buffer overflow creates an out-of-bounds write.”
A patch for the vulnerability was released by MediaTek in March 2024, although the likelihood of exploitation has increased with the public availability of a proof-of-concept (PoC) exploit as of August 30, 2024.
Source: TheHackerNews