North Korean Hackers Target Crypto Firms with Hidden Risk Malware on macOS – OfficialSarkar
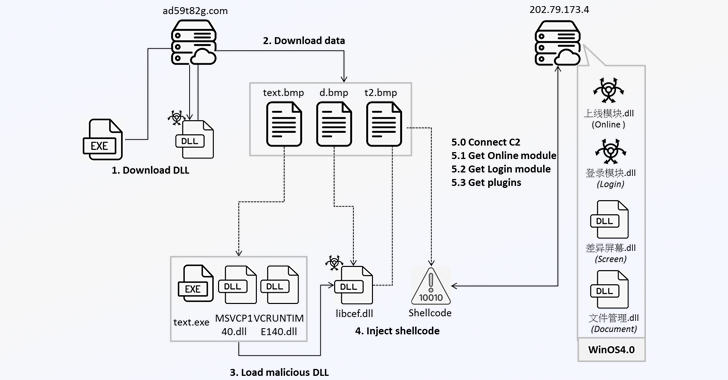
A threat actor with ties to the Democratic People’s Republic of Korea (DPRK) has been observed targeting cryptocurrency-related businesses with a multi-stage malware capable of infecting Apple macOS devices. Cybersecurity company SentinelOne, which dubbed the campaign Hidden Risk, attributed it with high confidence to BlueNoroff, which has been previously linked to malware families such as…



![RRC NFR Sarkari Result Recruitment Notification 2024 Out for 5647 Post [Career]](https://officialsarkar.in/wp-content/uploads/2024/11/Railway-RRC-NFR-Apprentice-Recruitment-2024-768x432.jpg)