Protecting Tomorrow’s World: Shaping the Cyber-Physical Future – OfficialSarkar
The lines between digital and physical realms increasingly blur. While this opens countless opportunities for businesses, it also brings numerous challenges. In our recent webinar, Shaping the Cyber-Physical Future: Trends, Challenges, and Opportunities for 2025, we explored the different factors shaping the cyber-physical future. In an insightful conversation with industry experts, we discussed the most pressing security concerns of today and how to address them.
Allison J. Taylor, the founder and CEO of Thought Marketing LLC, unveiled trends and recommended strategies businesses can employ to proactively bolster their security amidst evolving cyber challenges. Cesar Salazar, COO of Claro Enterprise Solutions, delved into innovative solutions that could propel business tech forward. He emphasized cyber-physical convergence, the use of emerging technologies, and responsive security operations.
Below are the key takeaways from the webinar. These provide an overview of why businesses should be concerned about the cyber-physical future and the importance of staying informed about the risks it poses.
Impact of Technological Waves on Trends and Emerging Threats
The evolution of major technology trends helps companies prepare for the future, particularly the “AI wave” expected to define 2025 and beyond. New technologies initially spark excitement and rapid adoption followed by gradual refinement. As companies “dabble” with new technologies, they learn to extract unique business value and achieve competitive advantages from each tech “wave.”
Technological Waves: From Web to Cloud to AI
In Web 1.0, the early days of the internet, we saw companies rebranding with the “.com” appended to their brand names. Many companies then launched basic, static websites, which served mainly as placeholders. It was very rudimentary, but it enabled them to test how the internet could create business value. Over time, businesses gained deeper insights.
Today, the tech landscape has grown far beyond this phase into Web 3.0. Now, businesses can leverage blockchain, NFTs, real-time data communication, and advanced APIs. Cloud computing went from a vague concept to a foundational technology. Businesses are now able to manage complex, multi-cloud strategies for cost efficiency and redundancy.
Currently, we’re in the midst of the “AI wave,” where AI is practically everywhere. However, businesses still need to explore specific, actionable ways to harness it effectively.
Similar Progressive Waves on Consumer Tech Adoption
We also see progression in consumer tech adoption. Let’s take voice recognition, for example. Initially, businesses integrated voice commands into existing systems as a simple enhancement—like phone trees and automated messages. But as the technology matured, it became far more nuanced, now supporting AI integration and humanlike interactions.
E-commerce has also evolved. It has transformed from early individual websites into expansive platforms with dynamic pricing and personalized experiences. In the next wave, we see AI-driven image recognition, which combines voice, image, and AI. With this advancement, we’re also bound to see new regulatory issues emerge.
Understanding this progression is crucial for businesses strategizing for cyber-physical integration. We see how each wave of technology—from the early internet to AI—follows a pattern of initial adoption, refinement, and mastery. And perhaps most importantly, no matter how technology evolves, the fundamental need for robust security and adherence to regulatory frameworks persists.
Persistent Issues on Threats and Regulation
Despite each tech wave’s potential, the presence of security and regulatory concerns remains constant and becomes more complex with each wave. In Web 1.0, websites were vulnerable to defacement attacks. With the cloud wave, data security became a bigger concern, and regulations became stricter on how and where data is stored. Now that AI is in the picture, we’re battling with deepfakes and other sophisticated threats.
Four Trends in the Threat Landscape
Technological waves do not happen in isolation. There are overlays and interconnectivity between technologies that create gaps and security threats. Here are four trends we see impacting the threat landscape.
1. A Change in Scope: Hyperconnectivity has expanded the potential for security threats.
More and more businesses today rely on cloud-based platforms like Office 365 and collaborative tools like Slack. These connect hundreds of external organizations and enable thousands of users to exchange information. While they enhance productivity, they also increase risks.
This hyperconnectivity has changed the scope of the tech landscape but has also expanded the potential for security threats. For one, sensitive data can be widely accessible, even beyond organizational boundaries. This interconnected nature means organizations now face greater challenges in securing data and managing compliance across a web of connected services and partnerships.
2. Increase in Threat Volume: The volume of threats continues to grow.
According to Check Point Research’s 2024 report on cyber-attack trends, there was a 30% increase in the volume of threats from 2023 to 2024. While this number is debatable, what’s certain is that threats continue to increase and impact all organizations. Affecting organizations of all sizes, cyber threats leave no business immune to the risks they pose.
3. Broadening Sources of Threats: External influences and physical vulnerabilities heighten threat levels.
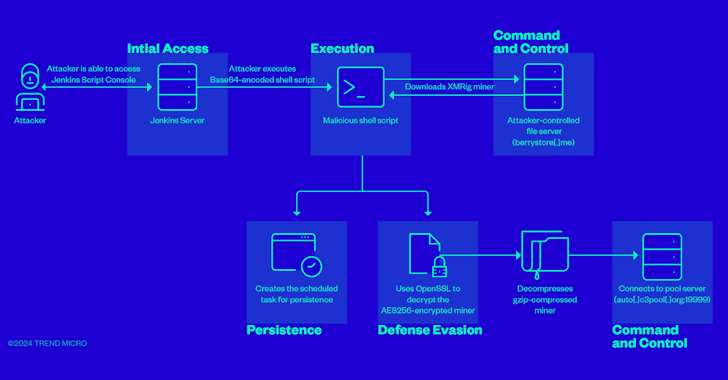
External influences, such as geopolitical tensions and elections, are heightening risk levels. Nation-states and political actors are increasingly involved in cyber activities. Then there are also issues on compromised physical security, social engineering attacks, vulnerability exploitation, supply chain infiltration, ransomware, and API exploitation. We see these threats targeting companies and infrastructure such as seen in recent attacks where malicious actors exploited consumer-grade routers and VPNs for coordinated attacks.
4. Shifts in Modality: Threats are shifting from cyber threats to physical threats to cyber-physical threats.
Threats now span beyond cyberspace. As we’ve mentioned, they now include physical security breaches (e.g., open doors to control rooms), phishing attacks, and social engineering. This makes it clear that cyber and physical security need to be tightly interwoven.
Businesses navigating the cyber-physical shift must adopt a balanced approach—strategically leveraging tech for productivity while prioritizing security and ethical considerations. It’s imperative for businesses to understand that everything is dynamic, and daily security practices remain essential.
The dynamic nature of cyber-physical threats necessitates robust security practices, exactly what the comprehensive approach of Claro Enterprise Solutions hinges on in addressing challenges.
Top Cyber and Physical Security Priorities for 2025
Based on insights from the current security threat landscape, we have identified five essential priorities organizations should address in 2025.
1. Continual Human-AI Collaboration
Although generative AI is trending, it has its limitations. Its real gains come from machine learning’s high-speed pattern recognition, productivity boosts, and continual human oversight. This approach requires ongoing expert intervention to shape workflows, ensure moral guardrails, and manage AI responsibly.
2. Enhancing Data Privacy
Hyperconnectivity increases data exposure risks. In cloud-based environments, in particular, sensitive data becomes accessible across platforms like Office 365 and Slack. This underscores the importance of proactive data privacy measures that protect sensitive information.
3. Building Resilient Supply Chains
With increasing global interdependence, supply chains face more vulnerabilities. There is an inherent need for comprehensive risk management that secures not only internal networks but also interconnected components in the supply chain.
4. Proactive Threat Detection
Staying ahead of cyber threats involves integrating daily security practices with real-time monitoring and immediate response capabilities. The value of proactive investments becomes clearer when compared to reactive costs like ransom payments, which can far exceed the cost of prevention. Investing in proactive security measures ultimately reduces long-term expenses by mitigating potential losses associated with cyber and physical security incidents, especially as resource-limited organizations become increasingly targeted by sophisticated threats.
5. Cyber-Physical Security Preparedness
Integrating digital and physical security measures is crucial as cyber-physical threats evolve. This includes combining physical safeguards with cyber defenses to build a holistic framework that addresses vulnerabilities across both realms.
The Importance of Tech Assessment
At the beginning of the webinar, participants did a self-assessment to identify the current role of IT in their organization. Determining which of the three stances your team is on can help you better prepare an appropriate roadmap toward a cyber-physical security future.
- Survival Mode. A reactive stance where IT keeps operations running but is viewed more as a functional utility rather than a strategic asset.
- Smart Mode. A proactive stand where IT enables automation and drives efficiencies, thereby supporting organizational goals.
- Leadership Mode. IT is considered a key player in achieving KPIs and a driver of innovation, actively supporting business performance and competitive advantage.
Once you identify the role that IT plays in your organization, you can determine the right solutions that would empower your organization to thrive. Regardless of your current IT stance, there are innovative solutions that can prepare you for the cyber-physical future. Claro Enterprise Solutions offers such solutions designed to help organizations realize their vision.
Safeguards and Challenges to Cyber-Physical Implementation
Claro Enterprise Solutions supports business clients in navigating the waves of cyber-physical convergence. Here are key safeguards and essential strategies businesses should consider to stay prepared as we move further into the cyber-physical era.
Attack from All Fronts
To better understand the need for a cyber-physical approach, the factors that are impacting all organizations today include:
| Cyber Threats | Physical Vulnerabilities |
|
|
We see bad actors on all fronts. We also see the interconnected nature of these threats. For instance, AI in cyber defense is primarily a cyber resource, but it also impacts physical security when used in surveillance or automated responses. It’s the same with IoT vulnerabilities. IoT devices are often deployed in physical environments that make them susceptible to both physical and digital attacks. This interdependence underscores the importance of a cyber-physical security solution.
Safeguards Companies Should be Implementing
With the persistent challenge of cyber and physical threats from malicious entities exploiting vulnerabilities for financial gain, businesses must evaluate and implement these cyber-physical safeguards:
- Cyber-Physical Asset Discovery and Inventory Update. Identify all assets in the network and ensure full asset visibility within the network.
- Adoption Of Zero Trust Security Models and Micro-segmentation. Limit system access, including internal access, to minimize security breaches and reduce other security risks.
- Security Monitoring and Incident Response. Utilize a centralized security operations center (SOC) that integrates real-time alerts from both cyber and physical systems for 24/7 monitoring and rapid incident response.
- Increased Investment in Security Awareness Training. Conduct regular threat detection education to empower users to prevent vulnerabilities and address human errors as soon as they are detected.
- Governance and Risk Management. Implement clear policies to maintain compliance and conduct risk assessments to ensure all security layers, for both internal and external risks, work together cohesively.
- Preparation for Quantum Computing Threats. Stay ahead of future threats by adopting quantum-resistant encryption and other measures.
Challenges in Implementing Safeguards
Indeed, deploying the safeguards above is necessary. However, implementing them comes with several challenges, including:
- Resource Constraints. Many businesses are unable to balance financial and human resources to secure critical areas.
- Complexity of Implementation. Disparate systems, particularly those in legacy systems, are difficult to integrate.
- Privacy and Ethical Considerations. As cyber-physical solutions become more advanced, businesses must balance security with user privacy and ethical data usage.
- Vendor and Solution Management. The huge number of specialized solutions in the market makes it a challenge to find the right fit.
To address these challenges, businesses should consider an integrated and holistic approach to cyber-physical security. An approach that combines authentication, data protection, and situational awareness for proactive security management.
A Vision for the Future: The Claro Cyber-Physical Vision
Claro Enterprise Solutions’ vision for cyber-physical convergence is to create a fully integrated defense that unites cyber and physical security through real-time, data-driven monitoring and advanced technologies. Our approach centers on a seamless “Alerts Hub” that consolidates data from digital and physical systems, providing a unified view to detect and respond to threats immediately. By leveraging AI Video Analytics, IoT, cyber security solutions, Zero Trust networking, and managed detection and response (MDR), our aim is to strengthen organizations’ resilience, ensuring they’re prepared for increasingly complex cyber-physical threats.
Our vision emphasizes adaptability for various business needs, from enhancing data protection and employee training to innovative, proactive security strategies, such as preparation for quantum computing threats. Our solutions, which are managed through a 24/7 Security Operations Center (SOC), offer businesses a holistic, scalable approach to security that not only protects but also advances their competitive edge.
Tech Solutions from Claro Enterprise Solutions
To enable businesses to launch their cyber-physical implementation plans, Claro Enterprise Solutions offers three essential tech solutions. These are designed to streamline and secure your organization’s digital operations. These innovative solutions help modern enterprises enhance security, productivity, and operational efficiency.
Collaboration Security Management
This integrated solution provides expert oversight to secure collaborative platforms, like Microsoft 365, against data breaches and compliance risks. Through continuous assessments and guided remediation, it ensures data protection and helps manage exposure risks. It empowers organizations to focus on productive, secure collaboration without sacrificing compliance.
Cloud Backup
With a multi-SaaS backup and restore solution, Claro Enterprise Solutions’ Cloud Backup protects data across multiple cloud applications. This comprehensive backup solution ensures that critical business data remains secure and easily recoverable in case of a breach or data loss. This gives organizations confidence in their data protection and continuity plans.
Microsoft 365 Migration Services
Claro Enterprise Solutions’ migration services facilitate a seamless transition to the Microsoft 365 platform. With a smooth migration, organizations can consolidate their digital workspaces with minimal disruption. This ensures an efficient shift that supports the continuity of operations.
As a single-source IT solutions provider, Claro Enterprise Solutions helps businesses independently implement, monitor, and manage their technology solutions. With these new products, we offer critical support for organizations looking to scale and innovate securely in a hyperconnected landscape.
Protect Your Organization, Arm Yourself with The Right Solutions
The insights shared in this webinar provide a practical guide on how businesses can prepare for the cyber-physical future. 2025 is just around the corner and there is a critical need for businesses to forge strategies aligned with emerging security trends.
To protect your organization from threats and challenges, arm yourself with knowledge of the latest cyber-physical solutions. Watch the full recording of the webinar, Shaping the Cyber-Physical Future: Trends, Challenges, and Opportunities for 2025, to learn more about what’s happening in the industry and how Claro Enterprise Solutions supports organizations looking to scale, just like yours.
Source: TheHackerNews