Hackers Leveraging Cloudflare Tunnels, DNS Fast-Flux to Hide GammaDrop Malware – OfficialSarkar
The threat actor known as Gamaredon has been observed leveraging Cloudflare Tunnels as a tactic to conceal its staging infrastructure hosting a malware called GammaDrop.
The activity is part of an ongoing spear-phishing campaign targeting Ukrainian entities since at least early 2024 that’s designed to drop the Visual Basic Script malware, Recorded Future’s Insikt Group said in a new analysis.
The cybersecurity company is tracking the threat actor under the name BlueAlpha, which is also known as Aqua Blizzard, Armageddon, Hive0051, Iron Tilden, Primitive Bear, Shuckworm, Trident Ursa, UAC-0010, UNC530, and Winterflounder. The group, believed to be active since 2014, is affiliated with Russia’s Federal Security Service (FSB).
“BlueAlpha has recently started using Cloudflare Tunnels to conceal staging infrastructure used by GammaDrop, an increasingly popular technique used by cybercriminal threat groups to deploy malware,” Insikt Group noted.
“BlueAlpha continues to use domain name system (DNS) fast-fluxing of GammaLoad command-and-control (C2) infrastructure to complicate tracking and disruption of C2 communications to preserve access to compromised systems.”
The adversary’s use of Cloudflare Tunnel was previously documented by Slovak cybersecurity company ESET in September 2024, as part of attacks targeting Ukraine and various NATO countries, namely Bulgaria, Latvia, Lithuania, and Poland.
It also characterized the threat actor’s tradecraft as reckless and not particularly focused on stealth, even though they take pains to “avoid being blocked by security products and try very hard to maintain access to compromised systems.”
“Gamaredon attempts to preserve its access by deploying multiple simple downloaders or backdoors simultaneously,” ESET added. “The lack of sophistication of Gamaredon tools is compensated by frequent updates and use of regularly changing obfuscation.”
The tools are chiefly engineered to steal valuable data from web applications running inside internet browsers, email clients, and instant messaging applications such as Signal and Telegram, as well as download additional payloads and propagate the malware via connected USB drives.
- PteroPSLoad, PteroX, PteroSand, PteroDash, PteroRisk, and PteroPowder – Download payloads
- PteroCDrop – Drop Visual Basic Script payloads
- PteroClone – Deliver payloads using the rclone utility
- PteroLNK – Weaponize connected USB drives
- PteroDig – Weaponize LNK files in the Desktop folder for persistence
- PteroSocks – Provide partial SOCKS proxy functionalit
- PteroPShell, ReVBShell – Function as a remote shell
- PteroPSDoor, PteroVDoor – Exfiltrate specific files from the file system
- PteroScreen – Capture and exfiltrate screenshots
- PteroSteal – Exfiltrate credentials stored by web browsers
- PteroCookie – Exfiltrate cookies stored by web browsers
- PteroSig – Exfiltrate data stored by the Signal application
- PteroGram – Exfiltrate data stored by the Telegram application
- PteroBleed – Exfiltrate data stored by web versions of Telegram and WhatsApp from Google Chrome, Microsoft Edge, and Opera
- PteroScout – Exfiltrate system information
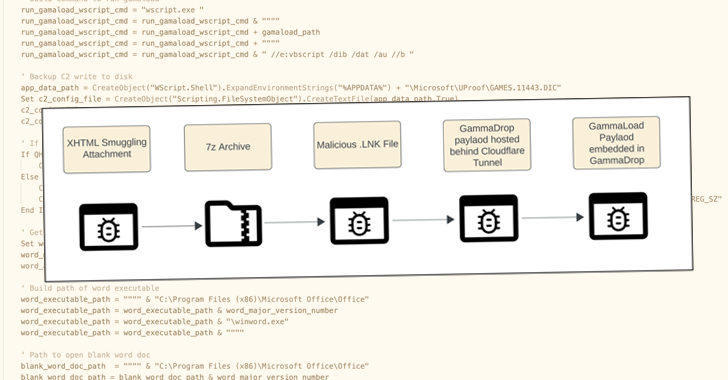
The latest set of attacks highlighted by Recorded Future entails sending phishing emails bearing HTML attachments, which leverage a technique called HTML smuggling to activate the infection process via embedded JavaScript code.
The HTML attachments, when opened, drop a 7-Zip archive (“56-27-11875.rar”) that includes a malicious LNK file, which makes use of mshta.exe to deliver GammaDrop, a HTA dropper responsible for writing to disk a custom loader named GammaLoad, which subsequently establishes contact with a C2 server to fetch additional malware.
The GammaDrop artifact is retrieved from a staging server that sits behind a Cloudflare Tunnel hosted on the domain amsterdam-sheet-veteran-aka.trycloudflare[.]com.
For its part, GammaLoad makes use of DNS-over-HTTPS (DoH) providers such as Google and Cloudflare to resolve C2 infrastructure when traditional DNS fails. It also employs a fast-flux DNS technique to fetch the C2 address if its first attempt to communicate with the server fails.
“BlueAlpha is likely to continue refining evasion techniques by leveraging widely used, legitimate services like Cloudflare, complicating detection for traditional security systems,” Recorded Future said.
“Continued enhancements to HTML smuggling and DNS-based persistence will likely pose evolving challenges, especially for organizations with limited threat detection capabilities.”
Source: TheHackerNews